Secure cluster head election algorithm and misbehavior detection approach based on trust management technique for clustered wireless sensor networks - ScienceDirect
![Amazon.com: [Upgraded] Anker SoundBuds Curve Wireless Headphones, 18H Battery, IPX7 Waterproof Bluetooth Headphones, Bluetooth 5.0, Built in Mic and Carry Pouch, SweatGuard Technology for Workout, Gym, Running : Electronics Amazon.com: [Upgraded] Anker SoundBuds Curve Wireless Headphones, 18H Battery, IPX7 Waterproof Bluetooth Headphones, Bluetooth 5.0, Built in Mic and Carry Pouch, SweatGuard Technology for Workout, Gym, Running : Electronics](https://m.media-amazon.com/images/I/513Pj6d7V8L._AC_SX522_.jpg)
Amazon.com: [Upgraded] Anker SoundBuds Curve Wireless Headphones, 18H Battery, IPX7 Waterproof Bluetooth Headphones, Bluetooth 5.0, Built in Mic and Carry Pouch, SweatGuard Technology for Workout, Gym, Running : Electronics

Mitigate Wormhole Attack and Blackhole Attack Using Elliptic Curve Cryptography in MANET | springerprofessional.de

Trust As a Means of Improving Corporate Governance and Efficiency in: IMF Working Papers Volume 2002 Issue 033 (2002)
Sensors | Free Full-Text | An Enhanced Three-Factor User Authentication Scheme Using Elliptic Curve Cryptosystem for Wireless Sensor Networks
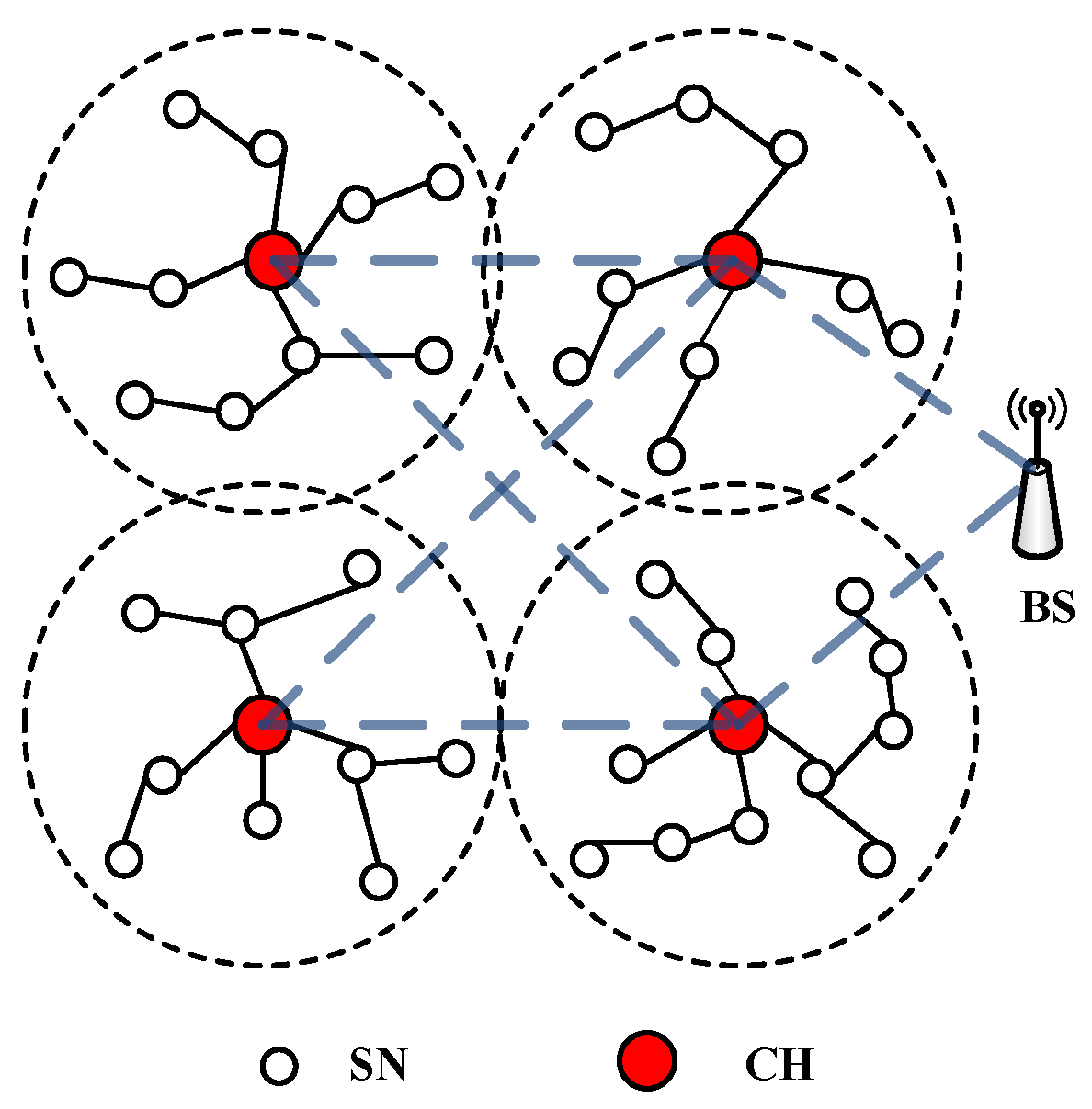
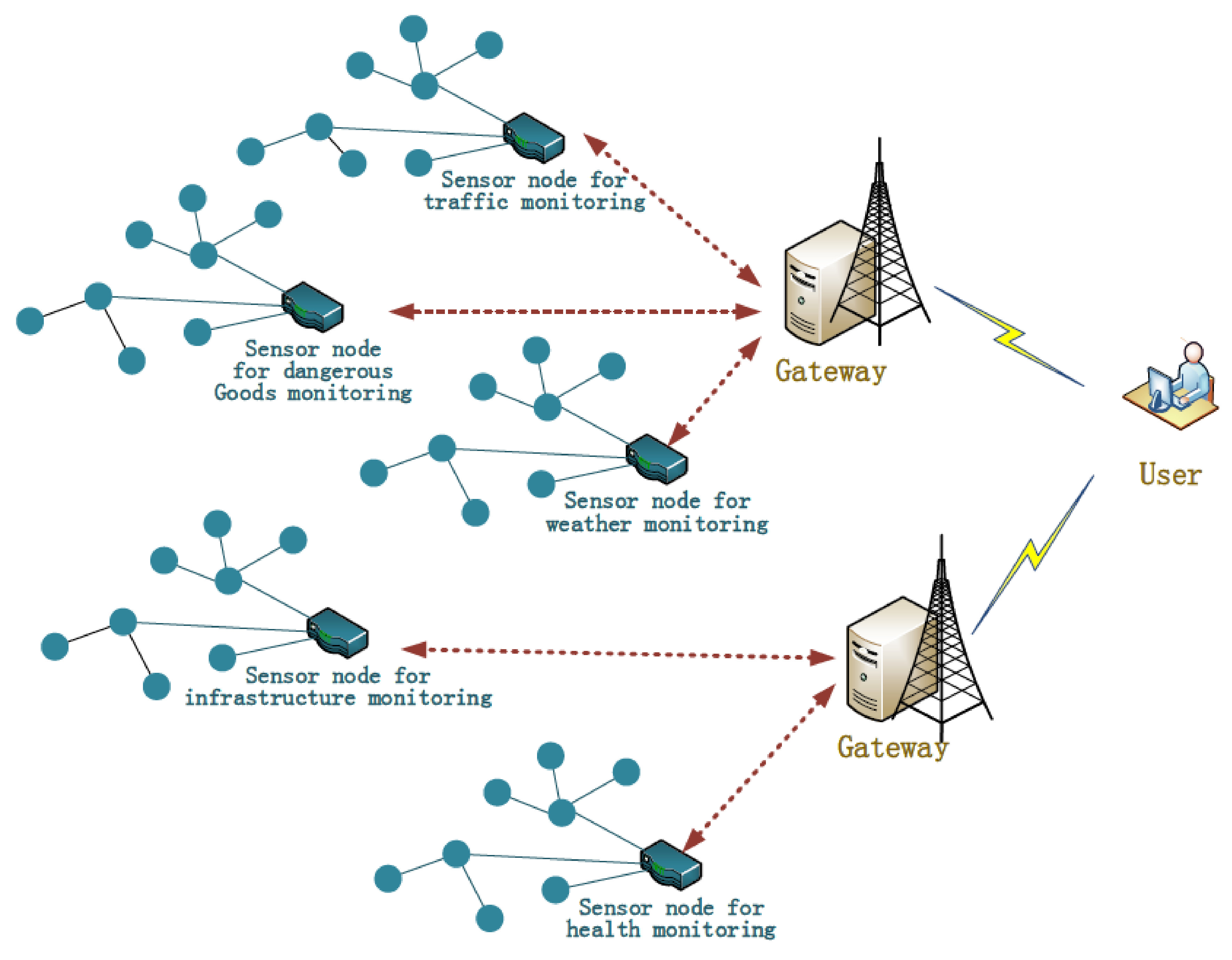
Sensors | Free Full-Text | A Protocol Layer Trust-Based Intrusion Detection Scheme for Wireless Sensor Networks | HTML
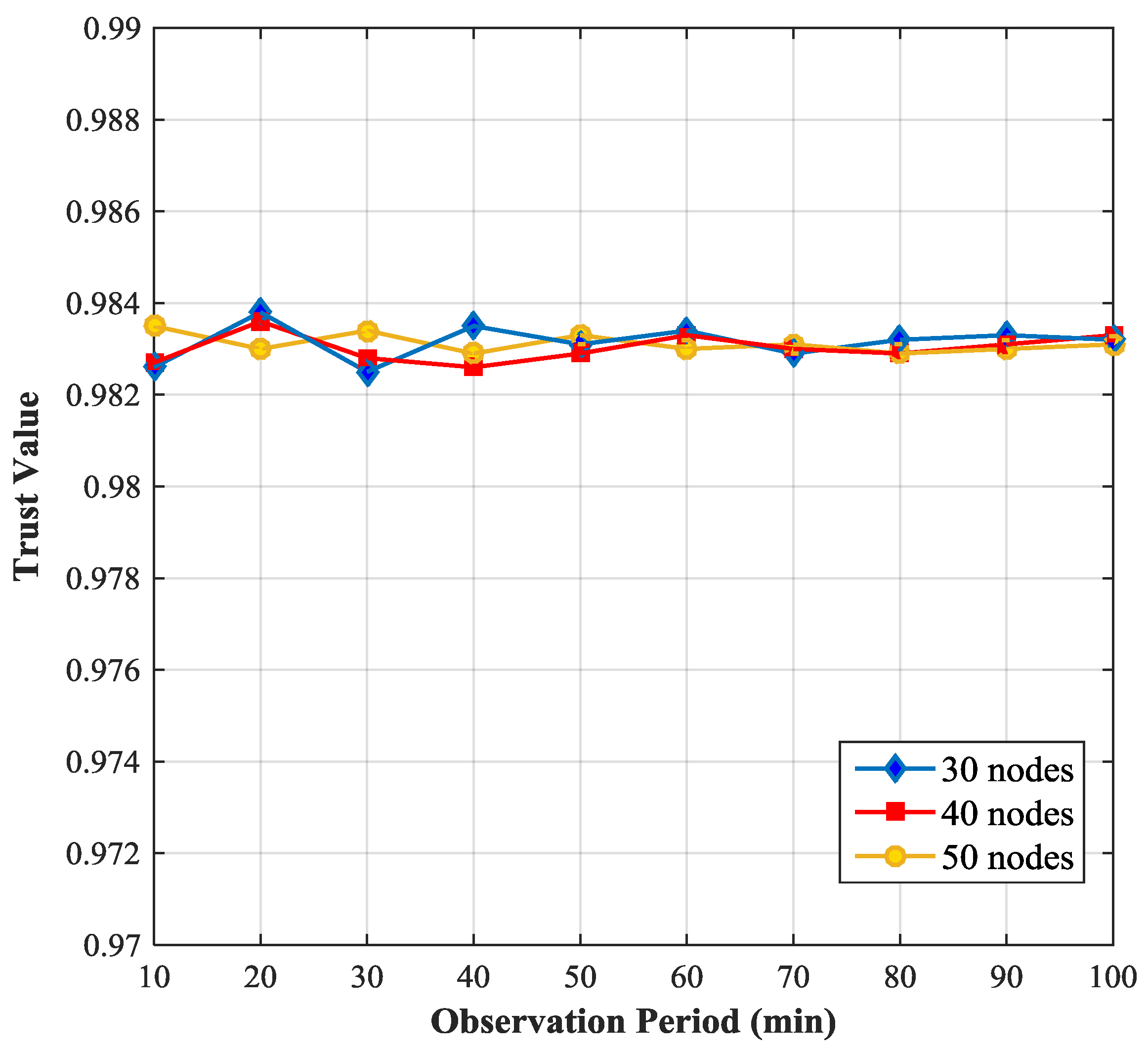
Sensors | Free Full-Text | A Protocol Layer Trust-Based Intrusion Detection Scheme for Wireless Sensor Networks | HTML









Wgg~~/s-l500.jpg)